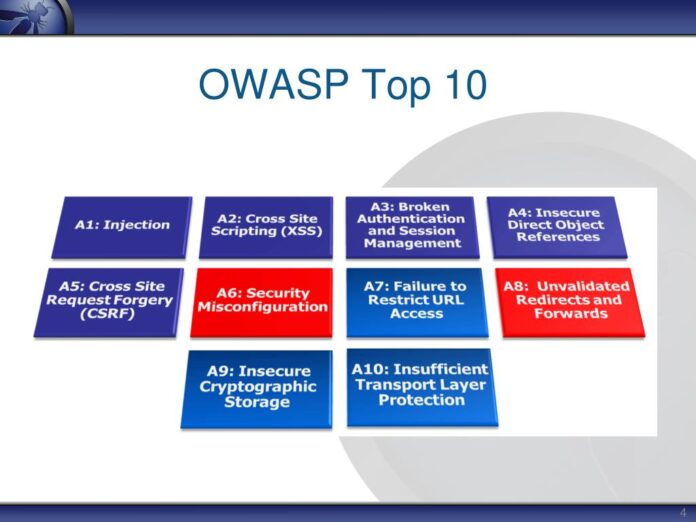
OWASP has provided guidance for developers, security professionals, and organizations in the field of web application security. At present, the OWASP Top 10 is an accepted standard that brings to light major vulnerabilities of web application security of the utmost importance. Here, we will look at the top 10 features of OWASP and why they are important in web application security.
Understanding OWASP
The term refers to the Open Web Application Security Project, often called OWASP, which is a global, not-for-profit organization oriented towards enhancing web application security. OWASP offers a plethora of resources, tools, and guidelines that can be used by organizations to build, sustain, and run secure web applications. Some of OWASP’s notable works include owasp top 10, a list of the top 10 security weaknesses that web applications are exposed to.
The OWASP Top 10 Features
Web Applications and OWASP Top 10. OWASP has identified these properties and continuously updates them based on the latest threats and vulnerabilities. Let’s explore each of the top 10 features and their significance:
Injection
- Feature: An injection denotes the capacity of attackers to send malicious input codes or commands to an application.
- Significance: Unauthorized access, loss of data, or manipulation of the application’s database can be caused by injection attacks such as SQL injection and command injection. Such attacks take advantage of vulnerabilities in input validation resulting in the execution of arbitrary commands and queries, leading to the compromise of sensitive data.
Broken Authentication
- Feature: Authentication and session management mechanisms that are not properly implemented open avenues for attacks such as session hijacking and account takeovers.
- Significance: User accounts and private information should be protected by proper authentication. Authentication failure may lead to compromised accounts, and possible data breaches. In cases when the authentication fails, allowing intruders to log in as legitimate users and obtain confidential information as well as proceed with illegitimate actions inside the application.
Sensitive Data Exposure
- Feature: Exposure involves the leak of important information like passwords, credit card information, or personal details as a result of poor encryption or improper management.
- Significance: Data breaches, identity theft, and legal and financial repercussions may ensue if sensitive data are not protected. Sensitive information is easily stolen when not enough effort is made towards encrypting and handling it. Failure to patch such vulnerability exposes users, both individuals and companies to attacks on their secrets.
XML External Entities (XXE)
- Feature: In a case of XXE attack, an attacker uses the loophole in the processing of XML input by an application without proper validation and thereby manages to access internal files and systems.
- Significance: This exposes the sensitive information making the whole application compromised. Attackers use malicious XML entities to alter the application’s behavioral properties, obtain secret information and get unauthorized access to internal application facilities. Such attacks are very dangerous to any application processing XML data with no strong security mechanisms in place.
Broken Access Control
- Feature: Broken access control is when an app doesn’t implement correct access control allowing for unlawful user access to sensitive data and functions.
- Significance: Poor access control can lead to unauthorized disclosure of information or even security attacks. However, poor implementation or enforcement of access control measures allows some users to access restricted features or information without permission. This may result in breaches of privacy, unauthorized changes or incidents of other security nature.
Security Misconfiguration
- Feature: Security misconfiguration means there are security holes due to misconfigured settings, too-open permissions, or defaults.
- Significance: Misconfigurations can create entry points, which can be abused by an attacker to gain unauthorized access or interrupt the function of an application. Examples of security misconfigurations include leaving open unnecessary ports, using of default passwords, and failure to update software components. Misconfigured systems are frequently exploited by attackers as easy entry points into their malicious practices.
Cross-Site Scripting (XSS)
- Feature: This is often achieved by injecting malicious scripts into web page requests viewed by other users.
- Significance: The problem is quite common and can lead to reputational harm and data theft. Malicious scripts may be injected into web applications that run in other users’ browsers. They can steal a session cookie and use it to log into the user’s account and perform unauthorized actions, deface web pages to destroy the user’s trust, and undermine the reputation of an organization.
Insecure Deserialization
- Feature: Insecure deserialization occurs when an application processes untrusted data during deserialization, leading to remote code execution and other security issues.
- Significance: Insecure deserialization may result in a full compromise of the system and unauthorized access to the application. Deserialization vulnerabilities may be exploited by attackers to execute arbitrary code, intrude, and modify application data. This is quite a serious danger for the application and its users as it relates to integrity and security.
Using Components with Known Vulnerabilities
- Feature: This poses a risk when a program uses old and insecure components, libraries, and frameworks.
- Significance: Some of the libraries or frameworks with known security loops, which are not fixed, can be considered vulnerable components. Such vulnerabilities can be exploited by attackers, undermining the security of software and allowing for data breaches or unauthorized access.
Insufficient Logging and Monitoring
- Feature: Security incidents are not detected and responded to on time due to insufficient logs and monitoring practices.
- Significance: Logging and Monitoring are critical aspects of securing network infrastructure in identifying security threats promptly and preventing data loss hence reducing damages. It may be difficult for an organization to detect suspicious activities, security breaches, or unauthorized access quickly without comprehensive logging and monitoring. Such a scenario would lead to slow incident management and greater loss from security breaches.
Conclusion
OWASP Top 10 is a significant source of information on common faults and security concerns, which makes it vitally important to web application security. Sticking by these principles would make it possible for companies to safeguard their web-based applications as well as other vital information from emerging threats.
Appsealing, as one of the most advanced security solutions for applications, complies with OWASP Top 10, ensuring maximum protection against weaknesses and hacker attempts. By having an overview of the principles laid down in the OWASP Top 10, an organization can strengthen its application security stance thereby protecting the users and data from likely dangers.